Download macOS Ventura ISO file
October 10, 2023
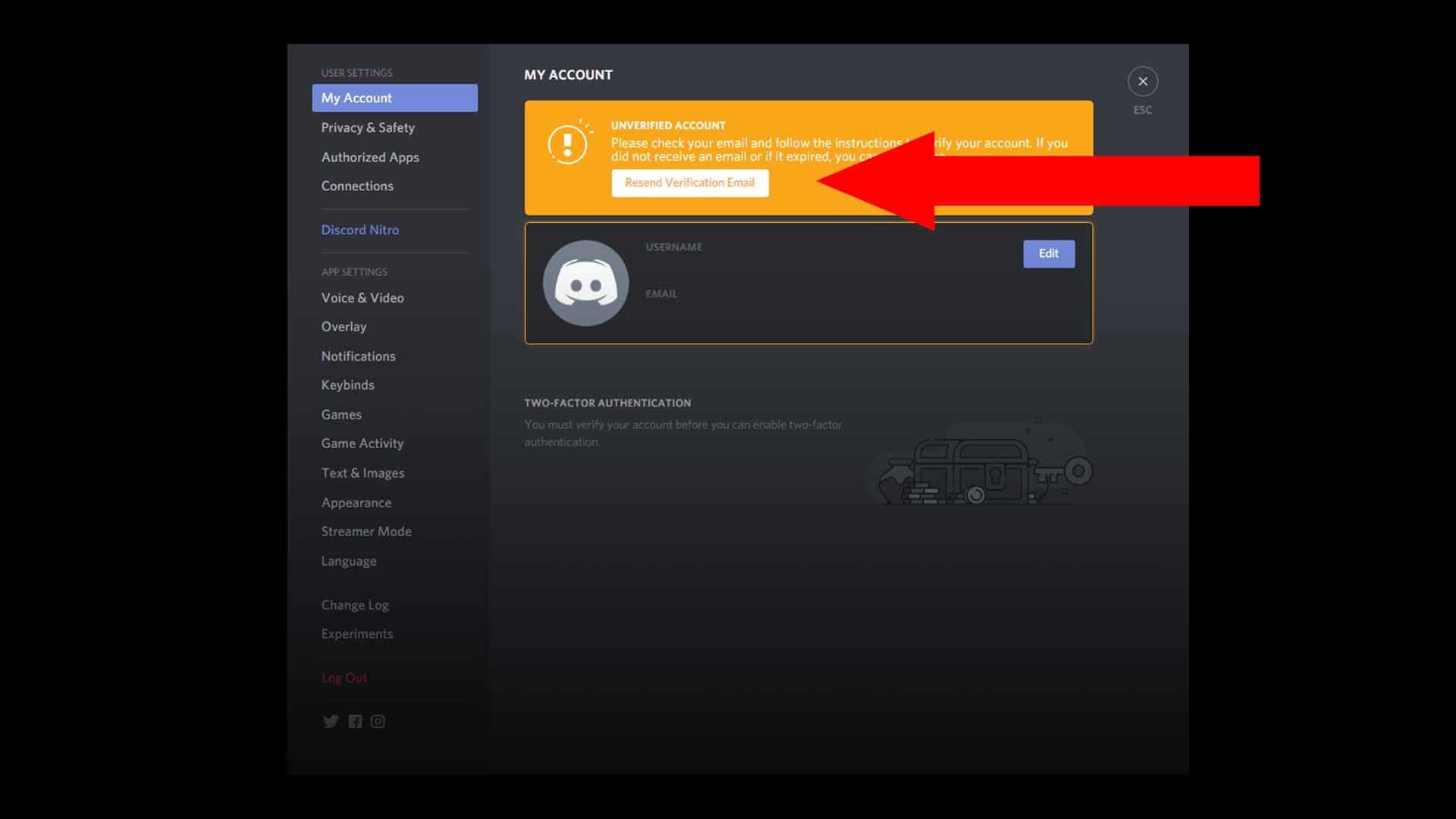
How To Bypass Mega Download Limits (2023 Update)
March 31, 2023
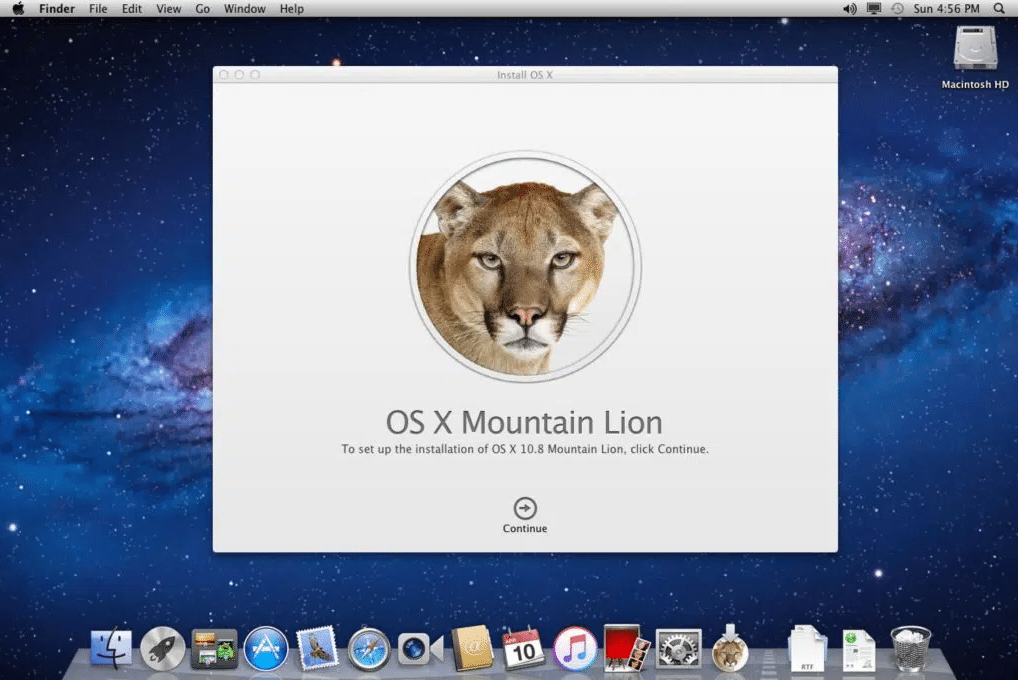
Download macOS X Lion 10.7 ISO and DMG Files
October 10, 2023
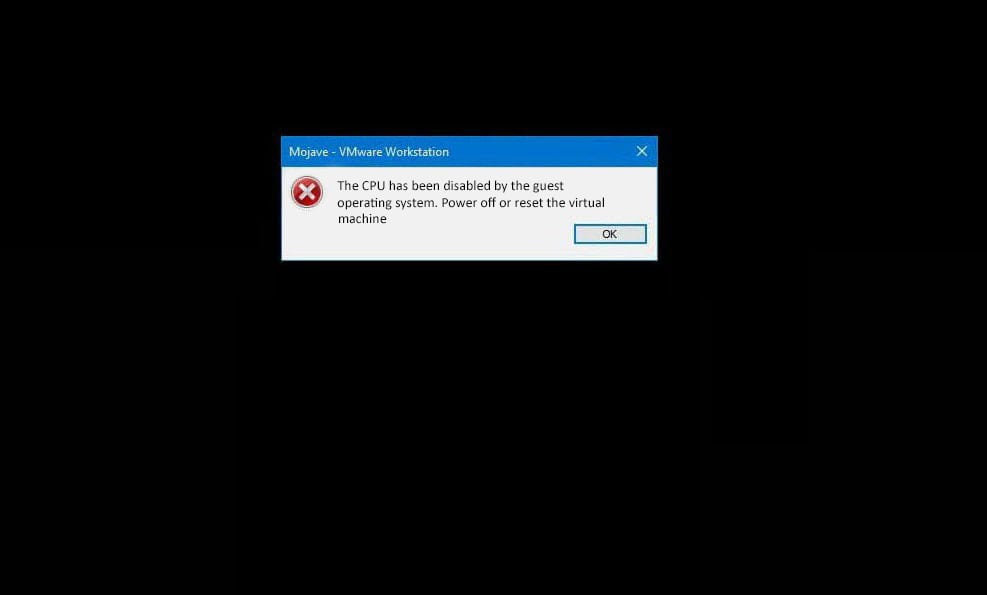
Install MacOS High Sierra On VirtualBox 2023 (Easy Method)
March 31, 2023
Top Healthcare SEO Strategies In 2024
April 26, 2024
Choosing the Right Link Shortener: Features to Look For
April 23, 2024
Why User-Centric Design Is So Important
April 16, 2024